The Managed DSPM Company


















Identify critical data and assess data security posture
Classify business-critical content
Protect sensitive and regulated data
Prevent overpermissioning
CISO
VP of Cybersecurity
CTO
Oil & Gas
CISO and VP of Infrastructure
F1000 Healthcare
Software Company
Principal Architect
We protect our customers with an agentless and easy to deploy platform that can work across unstructured and structured data without requiring large security teams.
Massive cloud migration and digital transformation are inarguably great for business, but managing all that data is like fighting a...
In today’s business landscape where digital transformation has almost reached ubiquity, data has become the backbone of almost every business. ...
As the transformation towards digital and cloud continues its rapid pace, data is becoming one of the most valuable assets...

Libero nibh at ultrices torquent litora dictum porta info [email protected]
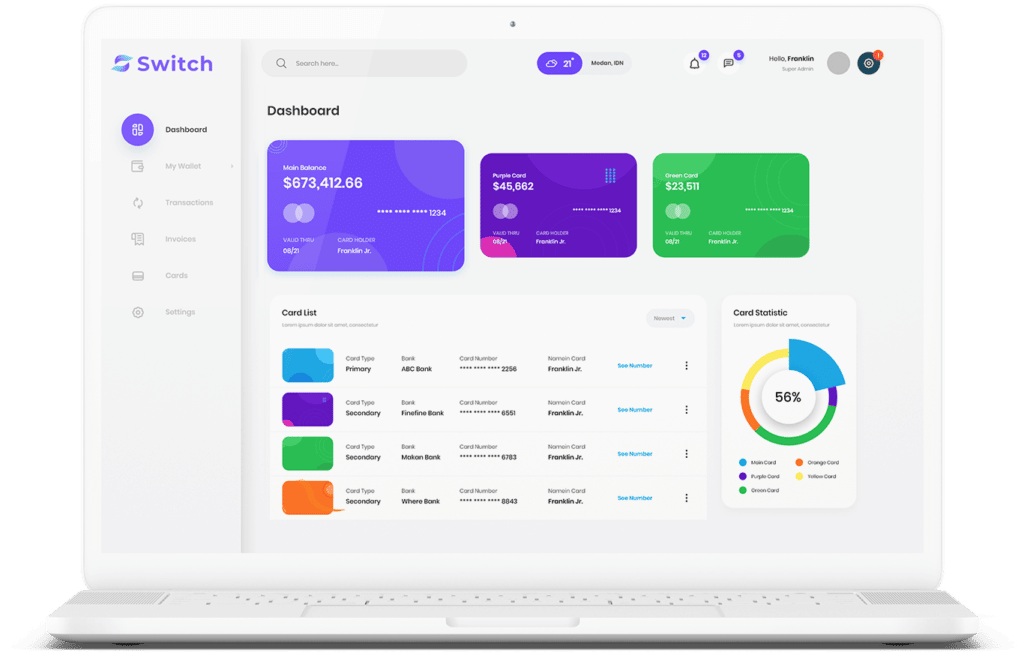
Start connecting your payment with Switch App.